Secure, Scalable Foundations for Mission-Critical Operations.
Cyber Arista designs, builds, and manages secure IT and cybersecurity environments that underpin modern, high-availability organisations. We help enterprises and governments protect critical systems, ensure operational resilience, and meet complex regulatory requirements across global jurisdictions.
Our integrated approach combines deep cybersecurity expertise with robust IT infrastructure design, delivering environments that are secure by design, resilient by default, and scalable for future growth.
Cyber Arista takes a holistic, lifecycle-based approach to cybersecurity and infrastructure. We assess risk, design
resilient architectures, implement best-practice controls, and provide ongoing managed services to ensure continuous protection and performance.
Security is embedded at every layer, from network and cloud infrastructure to endpoints, identity, and data, enabling organisations to operate with confidence in an evolving threat landscape.
Cyber Security Services
Security Architecture & Design
Design and implementation of secure enterprise architectures aligned with industry standards and regulatory frameworks. Our solutions address network segmentation, identity, access control, encryption, and secure cloud adoption.
Threat Detection & Response
24/7 monitoring, threat detection, and incident response through advanced security operations capabilities. We help identify, contain, and remediate threats before they impact business operations.
Governance, Risk & Compliance (GRC)
Support for regulatory compliance and security governance across sectors including government, finance, utilities, and telecommunications. We assist with policy development, risk assessments, audits, and ongoing compliance management.
Identity & Access Management (IAM)
Implementation of identity-centric security models, including privileged access management, zero trust principles, and secure authentication frameworks.
Data Protection & Privacy
Protect sensitive data across on-premises, cloud, and hybrid environments through encryption, access controls, backup, and recovery strategies.


- Managed IT & Infrastructure Services
- Security Operations & Monitoring
- Patch & Vulnerability Management
- Performance Optimisation & Capacity Planning
- 24/7 NOC & SOC Support
IT Infrastructure Services
Enterprise Network & Systems Engineering
Design and deployment of high-availability networks, compute, and storage platforms to support mission-critical workloads and geographically distributed operations.
Cloud & Hybrid Infrastructure
Secure migration and optimisation of cloud and hybrid environments, enabling flexibility, scalability, and cost efficiency while maintaining strong security and governance controls.
Resilient Infrastructure & Business Continuity
Architectures built for uptime, redundancy, and disaster recovery to support continuous operations in high-risk and regulated environments.
Data Centres & Edge Infrastructure
Design and support for data centre and edge environments, including high-density compute, remote site connectivity, and regional deployments.


IT Infrastructure Services
We work with organisations where security, uptime, and compliance are
non-negotiable, including:
- Government & Public Sector
- Telecommunications & Digital Service Providers
- Financial Services
- Utilities & Energy
- Large-Scale Infrastructure Operators
Why Cyber Arista?
Security-First Mindset
Every solution is designed with security embedded at its core, not added
as an afterthought.
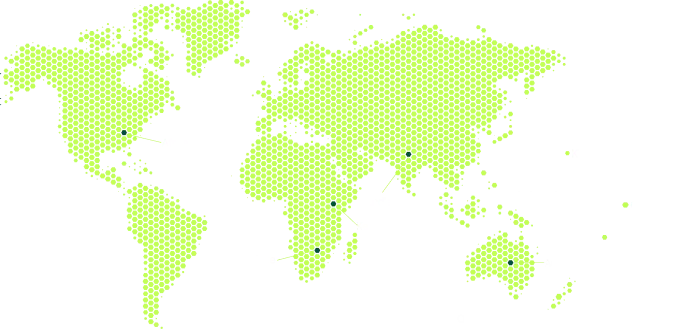
Global Delivery, Local Insight
We deliver across Australia, the Pacific, Africa, South and Southeast Asia,
and the Middle East, combining regional expertise with global best practices.
Vendor-Neutral Solutions
Our recommendations are driven by your operational and security
requirements, not vendor incentives.
Built for Scale & Compliance
We design environments that scale across regions while meeting the
demands of complex regulatory landscapes.